Back
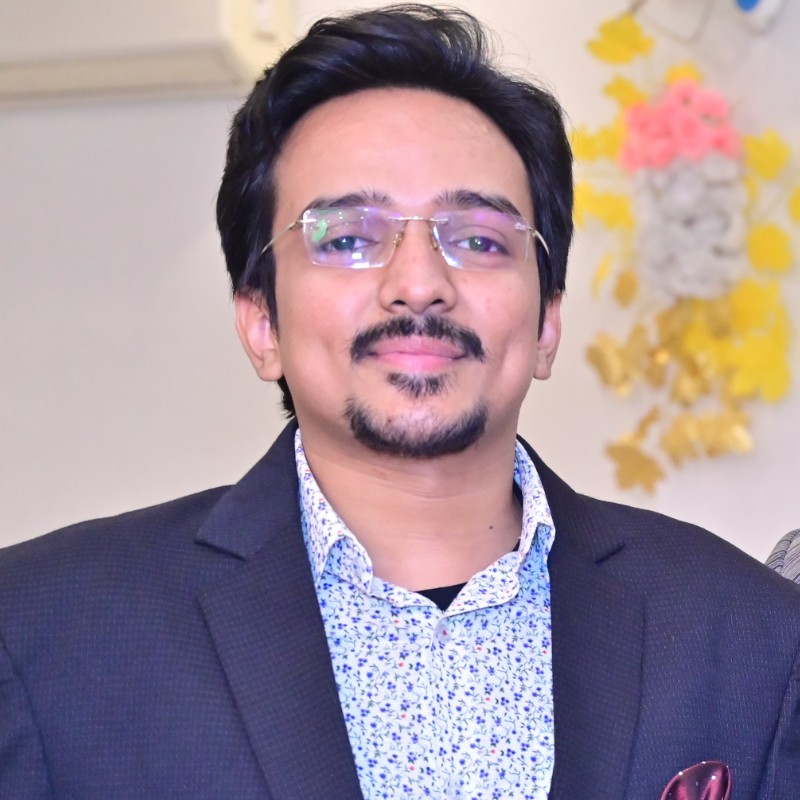
Vasvi Seth
Cyber Security Stude... • 1y
🚨 Attention, IT Professionals! 🚨 Beware of the latest security threat: PetitPotam! 🛡️ PetitPotam exploits vulnerabilities in Windows New Technology Local Area Network (LAN) Manager (NTLM), posing a significant risk to your network security. 🕵️♂️ This technique enables LAN-based attackers to launch authentication requests, potentially leading to unauthorized access and data breaches. 🔒
More like this
Recommendations from Medial
Account Deleted
Hey I am on Medial • 1y
🚨 Security Alert: The GodLoader malware has exploited vulnerabilities in the Godot Game Engine, compromising over 17,000 systems in just three months. This incident highlights the urgent need for robust cybersecurity measures within the gaming commu
See More
Sheikh Ayan
Founder of VistaSec:... • 1y
Top Metasploit Alternative Tools for Penetration Testing Metasploit is a powerful penetration testing tool, but several alternatives offer robust features for ethical hackers and security professionals: 1. Nmap – A fast network scanner for discover
See MoreSheikh Ayan
Founder of VistaSec:... • 1y
🔥 Top Exploitation Tools for Penetration Testing 🔥 🔹 Metasploit Framework – The go-to tool for developing, testing, and executing exploits efficiently. 🔹 Cobalt Strike – Advanced red teaming tool for post-exploitation, persistence, and lateral
See MoreSandeep Jangir
Cyber Security Profe... • 7m
🚨 Calling all Cybersecurity Trainers! 🛡️ I’m looking to connect with skilled and passionate Cybersecurity Trainers for an exciting opportunity. If you're experienced in delivering hands-on training in areas like: 🔹 Ethical Hacking 🔹 Network Sec
See MoreSheikh Ayan
Founder of VistaSec:... • 1y
🚨 Top IoT Vulnerabilities You Need to Know! 🚨 🔹 Weak Passwords & Default Credentials – Many IoT devices ship with default passwords that are easy to guess. 🔹 Unpatched Firmware – Outdated software can have security flaws that hackers exploit. 🔹
See MoreSheikh Ayan
Founder of VistaSec:... • 9m
🔍 Tired of Wireshark? Try These Powerful Alternatives! 🚨 Security Analysts, if you're looking for packet sniffers or network protocol analyzers beyond Wireshark, here are some top alternatives worth your radar: 🛠️ Top Wireshark Alternatives for
See MoreDownload the medial app to read full posts, comements and news.








/entrackr/media/post_attachments/wp-content/uploads/2021/08/Accel-1.jpg)