Back
Vasvi Seth
Cyber Security Stude... • 1y
🚨 Urgent Cybersecurity Alert: Log4Shell Vulnerability 🚨 Attention Medial community, Have you heard about Log4Shell? It's not just another tech jargon. This critical vulnerability is shaking up the cybersecurity landscape, and here's why: Log4Shell allows attackers to execute Java code on someone else’s computer or even worse, leak sensitive information. How? By exploiting a vulnerability in the popular logging library, Log4j, Log4Shell enables remote attackers to seize control of devices connected to the internet and unleash malicious code. The implications are staggering: from data breaches to system hijacking, Log4Shell poses a grave threat to digital security.
More like this
Recommendations from Medial
Vasvi Seth
Cyber Security Stude... • 1y
Ensuring robust cybersecurity measures is essential in today's digital landscape. Are you familiar with Server-Side Request Forgery (SSRF)? This vulnerability can enable attackers to manipulate server-side applications, granting unauthorized acces
See MoreVasvi Seth
Cyber Security Stude... • 1y
🔒 Understanding ZeroLogon: Microsoft's Netlogon Vulnerability 🔒 ZeroLogon, a critical vulnerability in Microsoft’s Netlogon authentication protocol, underscores the vital importance of robust cybersecurity measures. An authentication protocol ser
See MoreVenkatesh
Bussiness Developmen... • 1y
🚨 Exciting Opportunity Alert! 🚨 We are seeking a skilled Vulnerability and Penetration Tester for a critical project with the Ministry of Finance. If you're passionate about cybersecurity and ensuring the safety of critical systems, this role is a
See More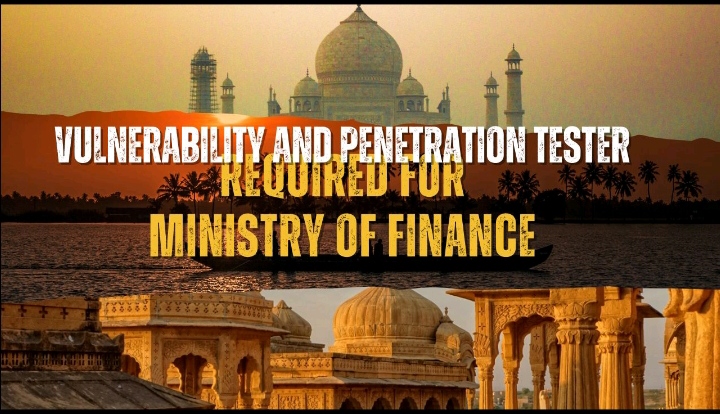
Vasvi Seth
Cyber Security Stude... • 1y
Security logging and monitoring failures can be detrimental to any organization's cybersecurity posture. Insufficient logging and monitoring capabilities pave the way for attackers to exploit vulnerabilities undetected, leaving organizations vulnerab
See MoreYashab alam
Founder ZehraSec • 10m
When the code runs perfectly and you’re too scared to refactor it.” 😅💻⚠️: #CoderLife #ItWorksDontTouch #DebuggingMagic #CodeMeme #devhumor #like #share #follow #comment #zehrasec #cybersecurity #findyou #python #hiring #ethicalhacking #infosec #cod
See More
Download the medial app to read full posts, comements and news.









/entrackr/media/post_attachments/wp-content/uploads/2021/08/Accel-1.jpg)