Back
Vasvi Seth
Cyber Security Stude... • 1y
🔒 Principle of Least Privilege: Enhancing Security and Efficiency🔒 In cybersecurity, the Principle of Least Privilege (PoLP) is paramount. It means granting users only the minimal access necessary to perform their tasks. By limiting permissions, we reduce the risk of data breaches and insider threats. Implementing PoLP not only fortifies our systems but also streamlines operations by preventing unnecessary access to sensitive information. Let's prioritize security by adopting this essential principle in our organizations.
More like this
Recommendations from Medial
Vasvi Seth
Cyber Security Stude... • 1y
🔒 Protecting Sensitive Personally Identifiable Information (SPII) is paramount in today's digital landscape. SPII encompasses data that requires even stricter handling guidelines to safeguard individuals' privacy and security. As we navigate the co
See MoreVasvi Seth
Cyber Security Stude... • 1y
🔒 Cybersecurity, also known as security, is paramount in today's digital age. It's the practice of safeguarding the confidentiality, integrity, and availability of information by fortifying networks, devices, and data against unauthorized access o
See MoreVasvi Seth
Cyber Security Stude... • 1y
🔒 As an entry-level security analyst, safeguarding organizational assets against threats is paramount. Understanding the various forms of threats is key to fortifying our defenses. Here are two common types every analyst should be vigilant about: •
See MoreVasvi Seth
Cyber Security Stude... • 1y
Protecting assets is paramount for any organization. Whether digital or physical, assets hold immense value. 📊 Digital assets, such as sensitive employee or client data like SSNs, dates of birth, and bank account details, demand robust safeguarding.
See MoreVasvi Seth
Cyber Security Stude... • 1y
Protecting organizational assets is paramount in today's digital landscape. To ensure comprehensive asset protection, organizations must address multiple potential threats: 1. External Risk: External threats, such as hackers and cybercriminals, pose
See MoreVasvi Seth
Cyber Security Stude... • 1y
🔒 Understanding ZeroLogon: Microsoft's Netlogon Vulnerability 🔒 ZeroLogon, a critical vulnerability in Microsoft’s Netlogon authentication protocol, underscores the vital importance of robust cybersecurity measures. An authentication protocol ser
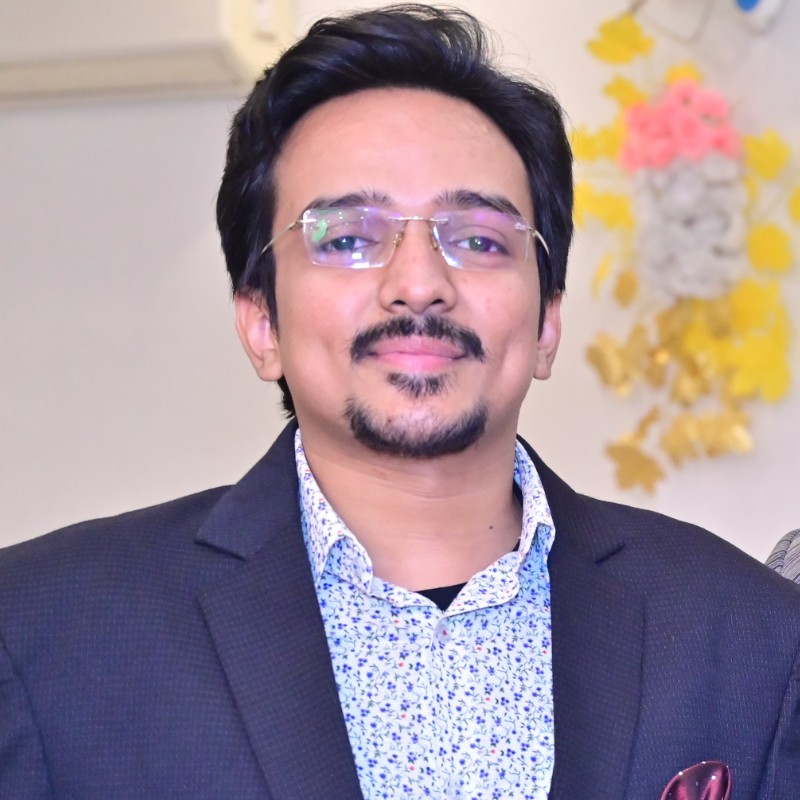
See MoreSheikh Ayan
Founder of VistaSec:... • 6m
🔒 Top Tools for Securing Your Server Room 🖥️ Protect your servers with the best tools in the industry: 1. CCTV Surveillance Systems 2. Biometric Access Control 3. Smart Locks & Keypads 4. Environmental Monitoring Sensors 5. Fire Suppression Syste
See MoreAccount Deleted
•
Urmila Info Solution • 8m
Founders are skipping security until it’s too late. Don’t be that startup. You’ve launched an AI tool. It works. Users love it. But what happens when: ❌ Servers get breached? ❌ User sessions are hijacked? ❌ Sensitive data leaks? At Opslify, we bui
See MoreDownload the medial app to read full posts, comements and news.








/entrackr/media/post_attachments/wp-content/uploads/2021/08/Accel-1.jpg)