Back
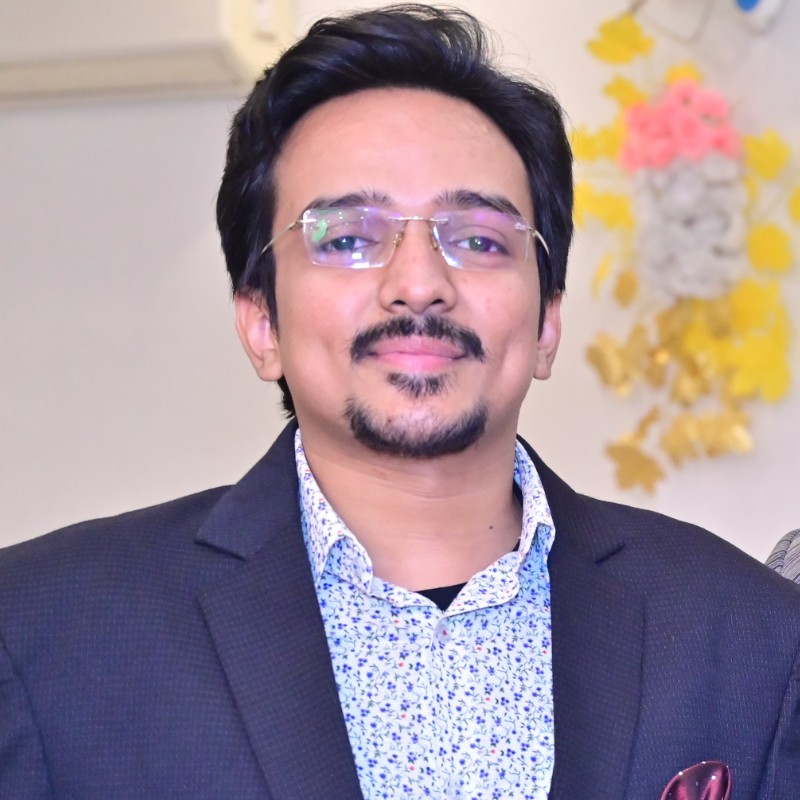
Vasvi Seth
Cyber Security Stude... • 1y
🔒 As an entry-level security analyst, safeguarding organizational assets against threats is paramount. Understanding the various forms of threats is key to fortifying our defenses. Here are two common types every analyst should be vigilant about: •Insider Threats: When staff members or vendors misuse their authorized access, it poses a significant risk to organizational data security. As analysts, we play a crucial role in detecting and mitigating such internal risks. • Advanced Persistent Threats (APTs): These stealthy threats involve threat actors maintaining unauthorized access to systems over prolonged periods. Vigilance and proactive measures are essential to combatting APTs effectively. Stay informed, stay vigilant!
More like this
Recommendations from Medial
Vasvi Seth
Cyber Security Stude... • 1y
🔒 Cybersecurity, also known as security, is paramount in today's digital age. It's the practice of safeguarding the confidentiality, integrity, and availability of information by fortifying networks, devices, and data against unauthorized access o
See MoreArun George
Startup Enthusiast |... • 11m
Nebula iXDR replaces complex and expensive security infrastructure with a simple, subscription-based solution that’s easy to deploy, scale, and manage. Designed for scalability and speed, Nebula iXDR automates threat detection and response, enabling
See More
Vasvi Seth
Cyber Security Stude... • 1y
Protecting organizational assets is paramount in today's digital landscape. To ensure comprehensive asset protection, organizations must address multiple potential threats: 1. External Risk: External threats, such as hackers and cybercriminals, pose
See MoreVasvi Seth
Cyber Security Stude... • 1y
Ensuring robust cybersecurity measures is essential in today's digital landscape. Are you familiar with Server-Side Request Forgery (SSRF)? This vulnerability can enable attackers to manipulate server-side applications, granting unauthorized acces
See MoreVasvi Seth
Cyber Security Stude... • 1y
Understanding the diverse landscape of cybersecurity threats is crucial in today's digital age. A threat actor, whether an individual or a group, can pose significant risks to the security of our systems and data. This risk encompasses various aspect
See MoreDownload the medial app to read full posts, comements and news.









/entrackr/media/post_attachments/wp-content/uploads/2021/08/Accel-1.jpg)