Back
Arun George
Startup Enthusiast |... • 11m
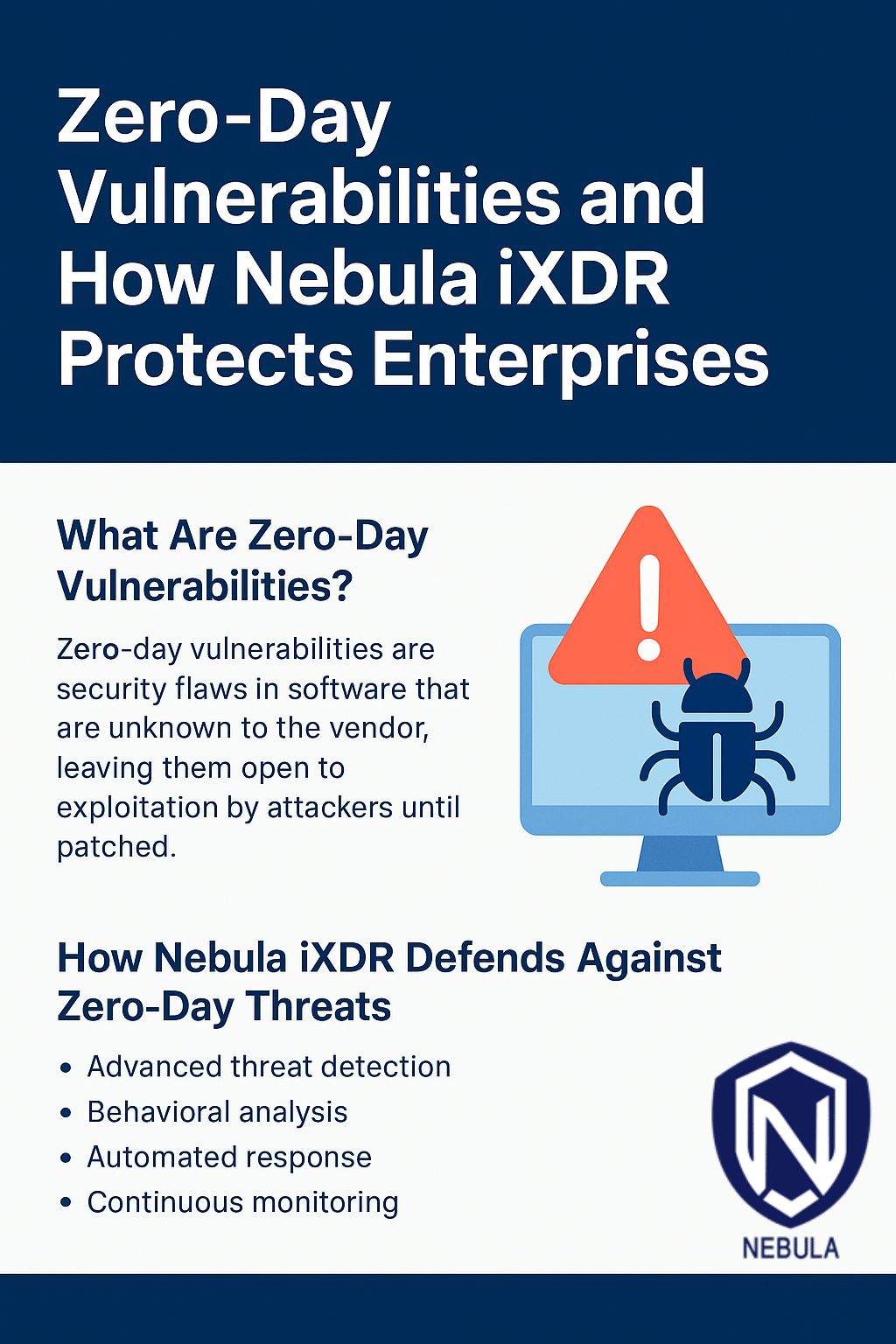
Nebula iXDR replaces complex and expensive security infrastructure with a simple, subscription-based solution that’s easy to deploy, scale, and manage. Designed for scalability and speed, Nebula iXDR automates threat detection and response, enabling Security Operations Centers (SOCs) to detect, investigate, and neutralize sophisticated attacks including zero-day threats, Advanced Persistent Threats (APTs), and obfuscated malware in real-time.
More like this
Recommendations from Medial
Vasvi Seth
Cyber Security Stude... • 1y
🔒 As an entry-level security analyst, safeguarding organizational assets against threats is paramount. Understanding the various forms of threats is key to fortifying our defenses. Here are two common types every analyst should be vigilant about: •
See MoreVasvi Seth
Cyber Security Stude... • 1y
Protecting organizational assets is paramount in today's digital landscape. To ensure comprehensive asset protection, organizations must address multiple potential threats: 1. External Risk: External threats, such as hackers and cybercriminals, pose
See MoreDataSpace Academy
Learn, Secure & Earn • 11m
What are the Top 3 Data Analytics Security Threats? Rising incidents of data breaches have put a big question mark on data safety. Added to these, there is the issue of poor Data quality and more. The blog here highlights major data analytics securi
See More
Download the medial app to read full posts, comements and news.










/entrackr/media/post_attachments/wp-content/uploads/2021/08/Accel-1.jpg)