Back
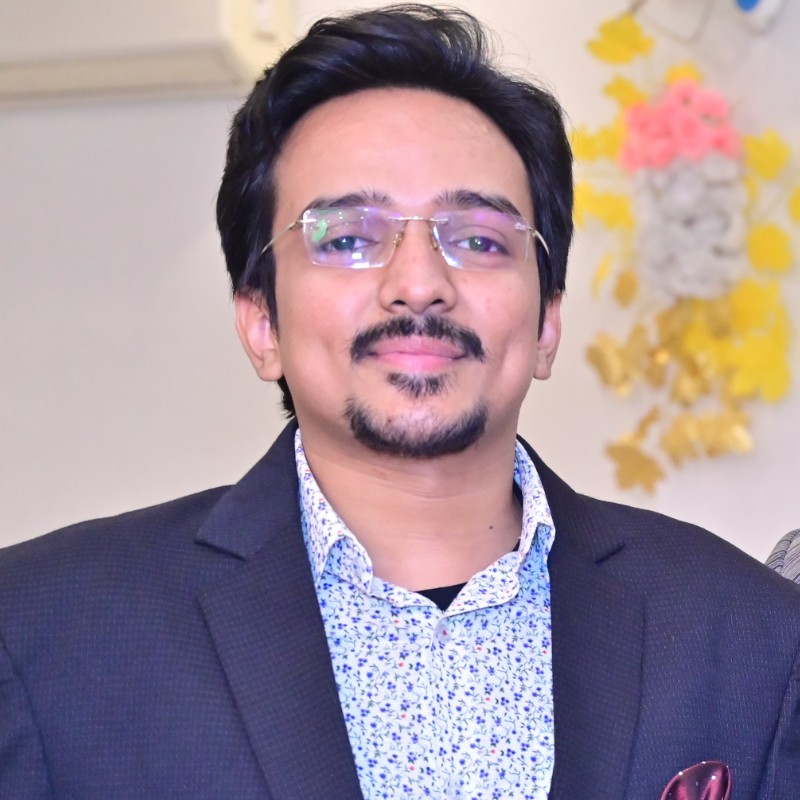
Vasvi Seth
Cyber Security Stude... • 1y
🔒 Elevate Your Cybersecurity Defense with Honey Pots! 🔒 In the fast-paced world of cybersecurity, staying one step ahead of threats is non-negotiable. Introducing Honey Pots – your secret weapon in the fight against cyber adversaries! 🛡️💻 What exactly are Honey Pots? They're decoy systems strategically positioned within your network to attract and divert potential attackers. By mimicking real assets, Honey Pots serve as a beacon, luring adversaries away from your critical infrastructure. But Honey Pots are more than just bait – they're a powerful tool for detecting both external threats and insider risks. By monitoring activity within the simulated environment, organizations gain invaluable insights into attack tactics and system vulnerabilities.🔒
More like this
Recommendations from Medial
Vasvi Seth
Cyber Security Stude... • 1y
Introducing Honey Pots – your secret weapon in the fight against cyber adversaries! 🛡️💻 What exactly are Honey Pots? They're decoy systems strategically positioned within your network to attract and divert potential attackers. By mimicking real as
See MoreVasvi Seth
Cyber Security Stude... • 1y
Security logging and monitoring failures can be detrimental to any organization's cybersecurity posture. Insufficient logging and monitoring capabilities pave the way for attackers to exploit vulnerabilities undetected, leaving organizations vulnerab
See MoreVasvi Seth
Cyber Security Stude... • 1y
Ensuring robust cybersecurity measures is essential in today's digital landscape. Are you familiar with Server-Side Request Forgery (SSRF)? This vulnerability can enable attackers to manipulate server-side applications, granting unauthorized acces
See MoreAccount Deleted
Hey I am on Medial • 1y
🚨 Security Alert: The GodLoader malware has exploited vulnerabilities in the Godot Game Engine, compromising over 17,000 systems in just three months. This incident highlights the urgent need for robust cybersecurity measures within the gaming commu
See More
Vasvi Seth
Cyber Security Stude... • 1y
🔒 Cybersecurity, also known as security, is paramount in today's digital age. It's the practice of safeguarding the confidentiality, integrity, and availability of information by fortifying networks, devices, and data against unauthorized access o
See MoreDownload the medial app to read full posts, comements and news.





/entrackr/media/post_attachments/wp-content/uploads/2021/08/Accel-1.jpg)