Back
NivroCorp
Your Partner in Web,... • 1m
You’re about to ship. Before you do, check these from a security perspective. These are things that break products later. Authentication Hash passwords with bcrypt. Rate limit logins. 2FA for admins. Why: weak auth becomes stolen accounts once users grow. Access control Check permissions on every request on the server. Why: most leaks come from users accessing data they should not see. Sessions Use short-lived tokens. HttpOnly cookies. Allow logout everywhere. Why: old sessions get reused and you lose control. Database No public access. Limited permissions. Tested backups. Why: one bad config or failed backup can wipe everything. Input validation Validate inputs. Use prepared queries. Why: simple requests can expose or corrupt data. Secrets No keys in repos. Use env variables. Why: leaked keys give full access to services. Logging Log logins and admin actions. Why: you need visibility when issues happen. Ship fast. Don’t ship blind. Need a security check? Dm me.
More like this
Recommendations from Medial
techorate
Let's decorate your ... • 1y
Why Azure AD Matters for Businesses Azure Active Directory (Azure AD) is more than just an authentication tool—it’s a comprehensive identity and access management solution that helps businesses: Automate User Access – Assign, modify, and revoke per
See MoreSheikh Ayan
Founder of VistaSec:... • 7m
🔐 5 Security Models Every Business Must Know (and How to Use Them!) Cyber threats are rising, and businesses that don’t secure their data are at risk. Here are 5 proven security models to protect your organization: 1️⃣ Bell-LaPadula (Confidentiali
See MoreSheikh Ayan
Founder of VistaSec:... • 1y
🚨 Top IoT Vulnerabilities You Need to Know! 🚨 🔹 Weak Passwords & Default Credentials – Many IoT devices ship with default passwords that are easy to guess. 🔹 Unpatched Firmware – Outdated software can have security flaws that hackers exploit. 🔹
See MoreChetan Bhosale
Software Engineer | ... • 1y
Understanding Access Tokens and Refresh Tokens in an Indian Scenario 🇮🇳: Access Token: Think of it as a cinema ticket 🎟️. It allows you to use an app (like a banking app) for a specific period. Refresh Token: Imagine having a special pass 🏷️. W
See MorePratik Raundale
Cloud Devops Enginee... • 22d
NAT Gateway vs NAT Instance in AWS If your instances are in a private subnet, they cannot access the internet directly. To allow outbound internet access, we use NAT (Network Address Translation). In Amazon Web Services there are two options: NAT
See More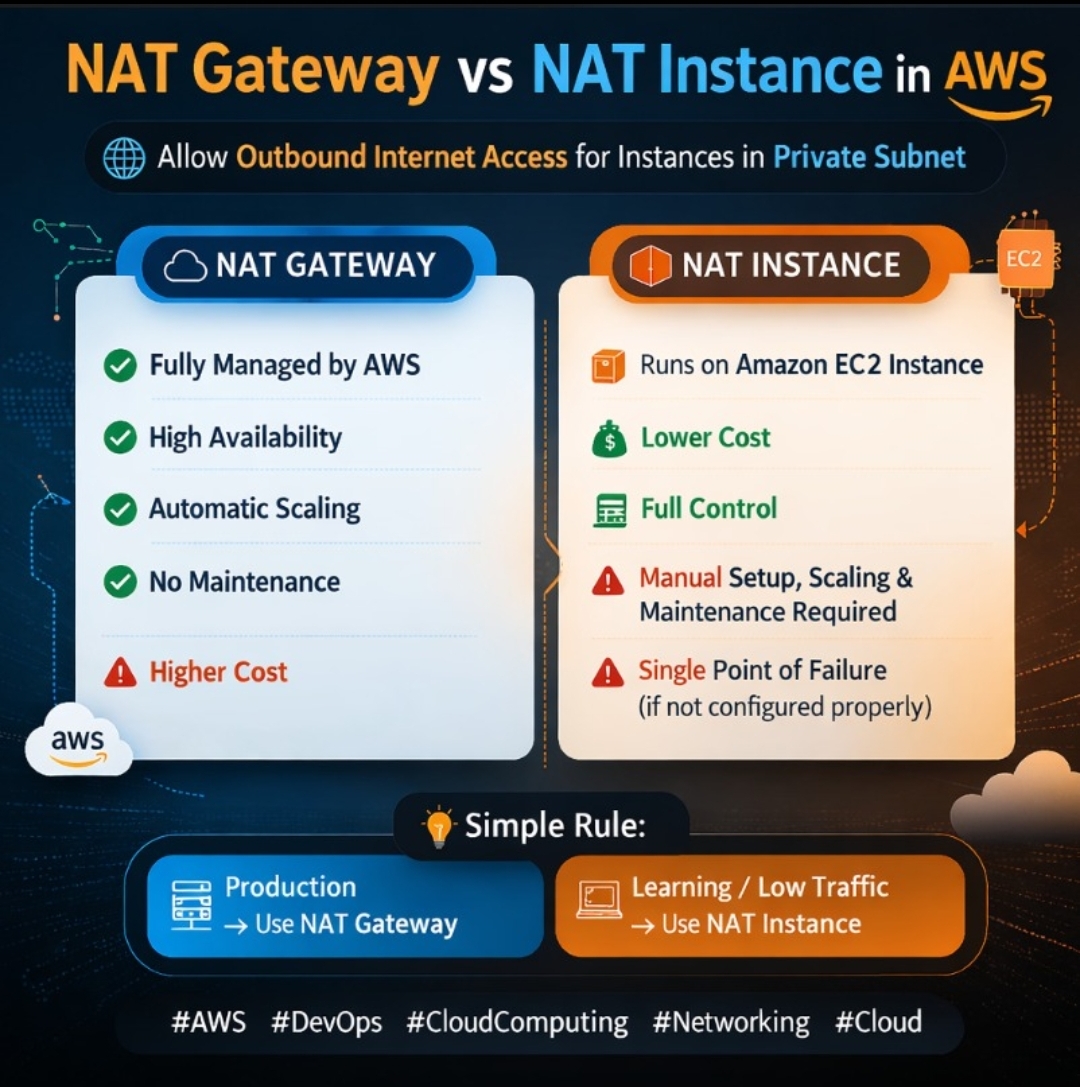
Download the medial app to read full posts, comements and news.











/entrackr/media/post_attachments/wp-content/uploads/2021/08/Accel-1.jpg)