Back
More like this
Recommendations from Medial
Vasvi Seth
Cyber Security Stude... • 1y
Protecting organizational assets is paramount in today's digital landscape. To ensure comprehensive asset protection, organizations must address multiple potential threats: 1. External Risk: External threats, such as hackers and cybercriminals, pose
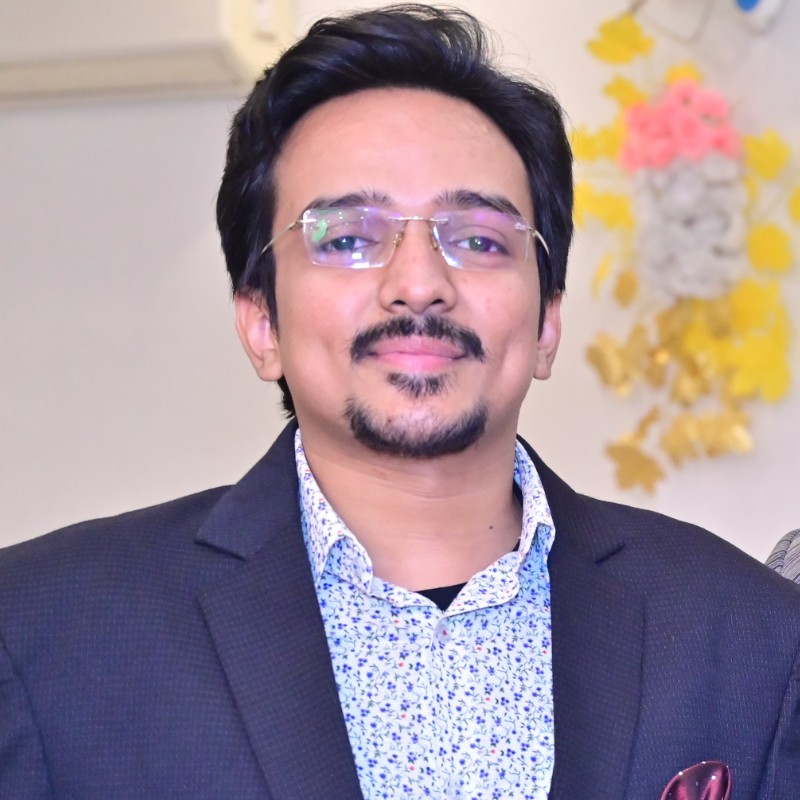
See MoreVansh Khandelwal
Full Stack Web Devel... • 1y
Security testing ensures that applications are free from vulnerabilities like SQL Injection, XSS, CSRF, and IDOR. SQL Injection occurs when unsanitized inputs allow attackers to manipulate database queries. This can be mitigated by using parameterize
See MorePranav padmanabhan
AI Data Scientist • 5m
AI browsers are evolving fast local agents, workflow automation, context-aware search. But as they gain deeper access (tabs, files, cookies, workspace), the attack surface expands. Privacy isn’t optional anymore. We need stronger guardrails: • Local
See MoreVamshi Yadav
•
SucSEED Ventures • 11m
Google DeepMind’s CaMeL: A Breakthrough in Stopping AI’s "Prompt Injection" Problem? For years, prompt injection attacks (where hidden instructions trick AI models into bypassing safeguards) have haunted developers. Despite countless fixes, no solut
See MoreDownload the medial app to read full posts, comements and news.












/entrackr/media/post_attachments/wp-content/uploads/2021/08/Accel-1.jpg)