Back
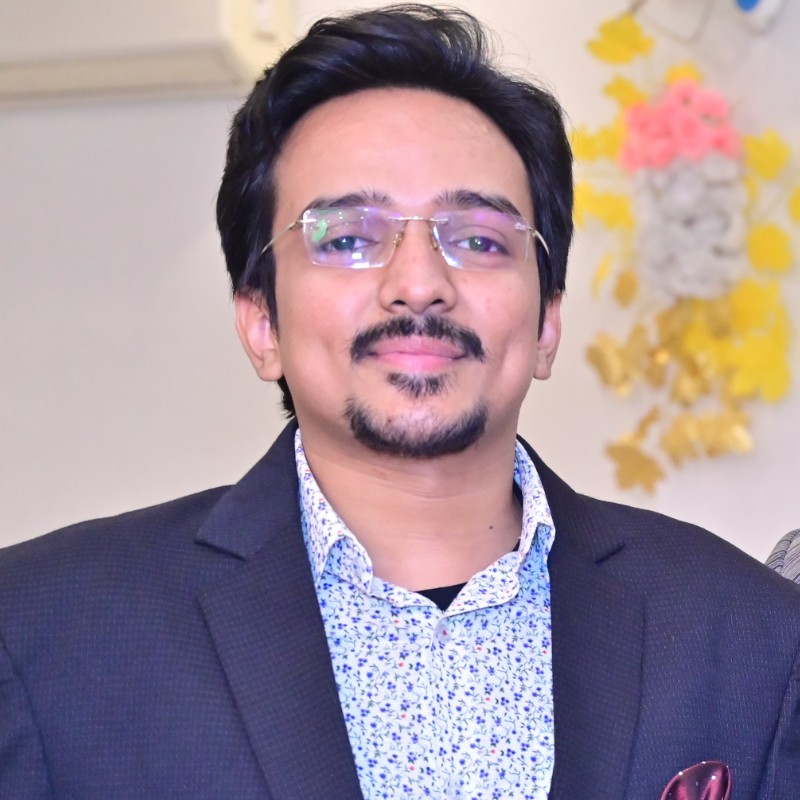
Anonymous 1
Hey I am on Medial • 1y
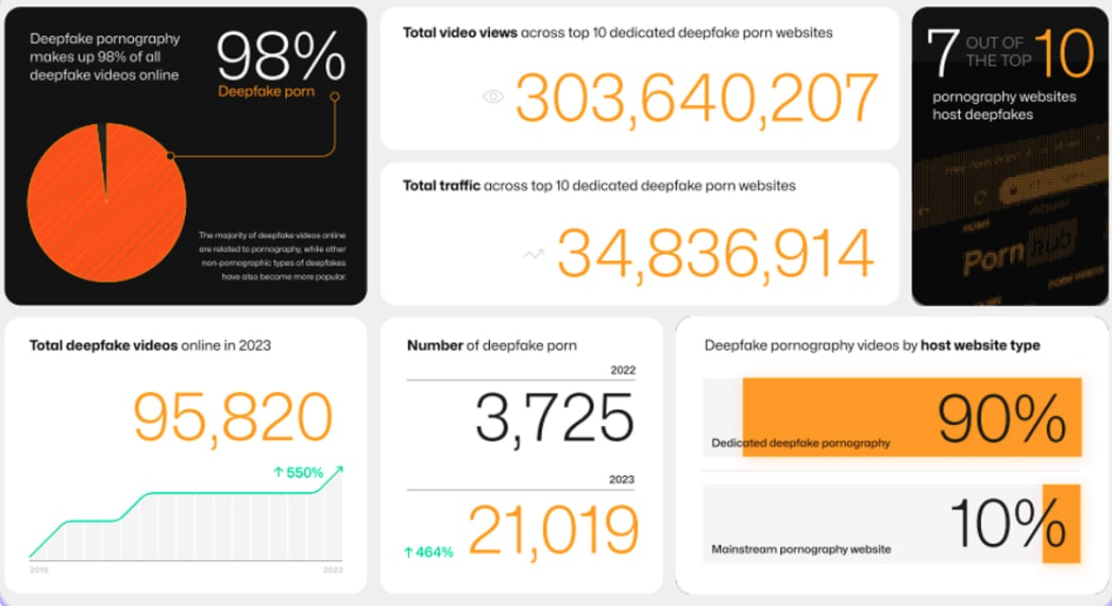
Should be, AI is indeed revolutionary but it should be controlled before massive misuse happens like in the case of Deepfakes, morphs, disruption of E-KYC etc.
More like this
Recommendations from Medial
Gautam Das
If I play, i play to... • 1y
Scientists say whatever safeties we create may be useless in preventing harmful AI from taking over the world. In fact, there is no current evidence that AI can be controlled safely, according to an extensive review, and without proof that AI can be
See MoreAjay D Nair
Fighting Fraud with ... • 8m
I have been seeing a lot of posts on AI making deep fakes of financial documents or id cards. Isn't there data driven models in Fraud Detection Tools to identify such deep fakes. Important financial documents and ID's which are usually used in kyc
See MoreNandhakishore
#entrepreneur • 1y
Yooo guyss looking for an cofounder to built an revolutionary product , he should have great knowledge and passion in programming. If interested let me know. It will be very gud if you are from south india.Only necessary condition is that should not
See MoreAnonymous
Hey I am on Medial • 1y
I think next civil war in India happens because of tax . We are facing this huge problem since 1947 and every government force only middle class people's for tax . According to reports only 3.5% people in India paying tax and other are just enjoying
See MoreDownload the medial app to read full posts, comements and news.











/entrackr/media/post_attachments/wp-content/uploads/2021/08/Accel-1.jpg)