Back
Anonymous 1
Hey I am on Medial • 1y
Gotcha. Even i got curious from your question and looked it up, it says: Hashing and encryption are both fundamental computer system operations that change raw data into a different format. However, they differ in the following ways: Purpose Hashing is used to ensure data integrity, while encryption is used to protect data privacy. Reversibility Encryption is reversible, but hashing is irreversible. Data size Hashing is used to store large amounts of data, while encryption is used to protect small amounts of data in transit.
Replies (1)
More like this
Recommendations from Medial
TREND talks
History always repea... • 1y
🤖 Windows 11 BitLocker Encryption has been BYPASSED! 👨💻 Researchers have shown a method to bypass bitlocker using physical attacks. This attack is done by checking and capturing contents of RAM while the computer boots up. Why? Because bitlocker
See More
Anonymous
Hey I am on Medial • 4m
Arattai is a fast-evolving Indian messenger from Zoho with rich features but partial message encryption today, WhatsApp is the most feature-complete and ubiquitous with full end-to-end encryption and strong safety tools but heavier metadata collectio
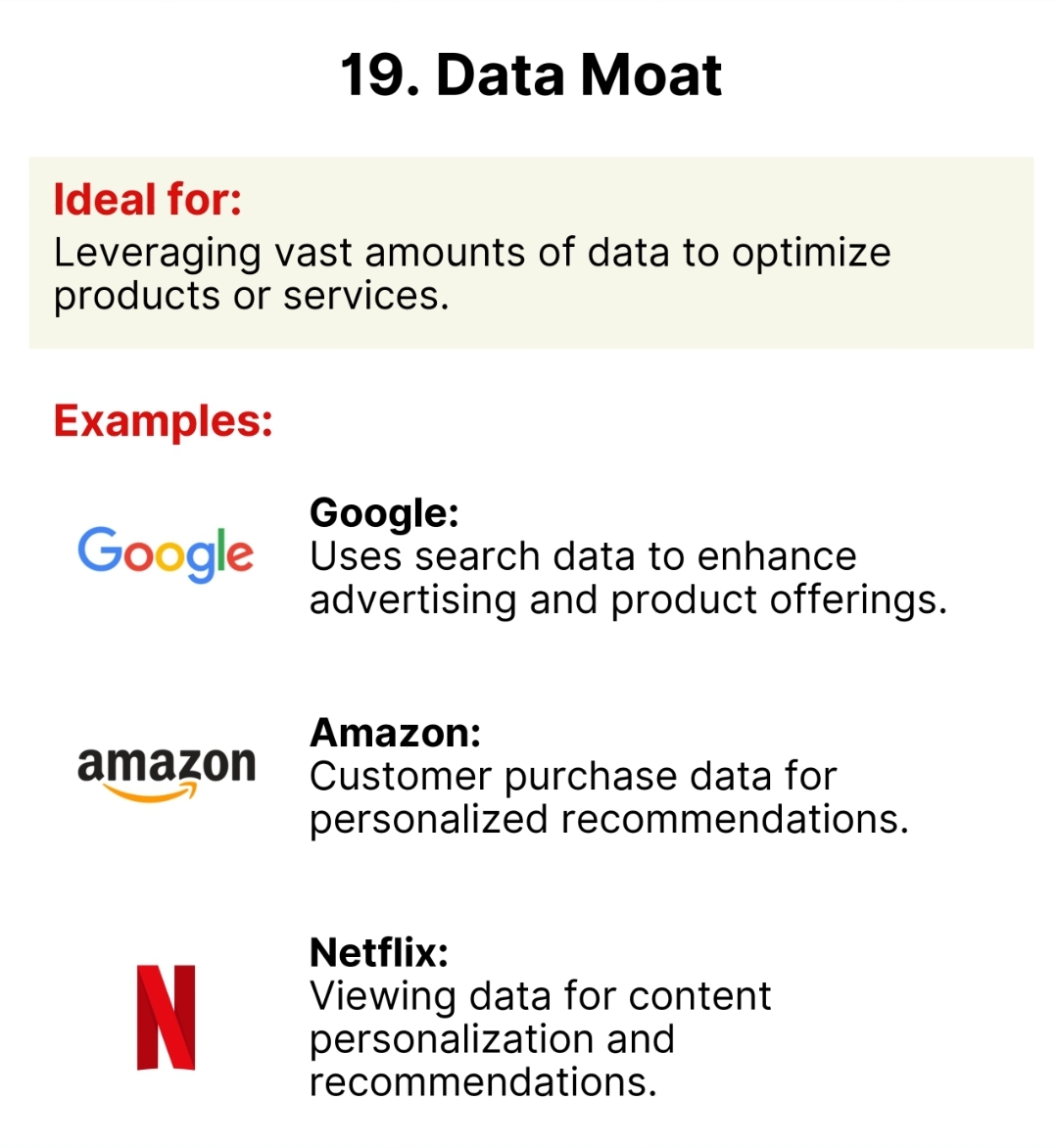
See MoreThakur Ambuj Singh
Entrepreneur & Creat... • 11m
📊 Data Moat: The secret weapon of tech giants! ⚡ Google, Amazon and Netflix harness vast amounts of data to personalize experiences, optimize services and dominate their industries. 🚀💡 Knowledge is power and these companies have plenty of it! 🔥
Vasvi Seth
Cyber Security Stude... • 1y
Delving into Communication Protocols: The Pillars of Network Transmission Communication protocols are fundamental to the exchange of information across networks. They govern how data is transmitted between devices, ensuring that communication is eff
See MoreTanay Shandilya
Cyber Risk • Web Dev... • 1y
So here is an idea I got while stuck in traffic… What if I can create a DbaaS product that has built in features like data anonymisation, pseudonymsation, built in data record encryption, masking woth custom masking markers and can provide analytics
See MoreDownload the medial app to read full posts, comements and news.











/entrackr/media/post_attachments/wp-content/uploads/2021/08/Accel-1.jpg)