Back
Arnav Aggarwal
Love to Code | React... • 10m
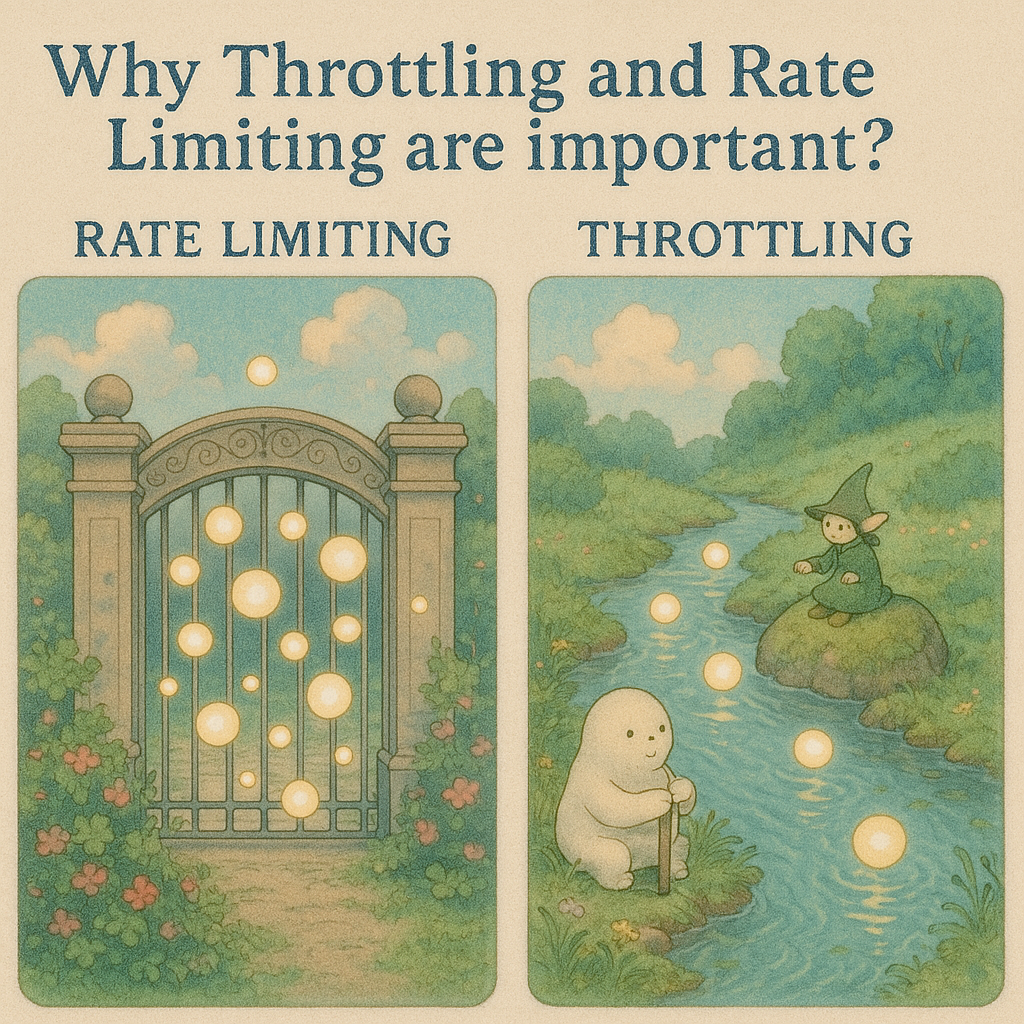
Hit an unexpected 'rate limit' message while creating Studio Ghibli-style images on ChatGPT? You weren't alone.This is a great example of API traffic management techniques like Rate Limiting and Throttling. ➡️Rate Limiting - Sets a hard cap; requests are blocked 🚫 once the limit is reached until the timer resets – like being locked out after too many wrong password attempts. - Prevents abuse, ensures fair usage, and protects servers from overload. ➡️Throttling - Queues or delays excess requests ⏳, processing them at a controlled pace. Queued requests may eventually be rejected if delayed too long. Example: Rate Limiting is like riding 5 rollercoasters max 🎢, while Throttling slows the queue by pacing rides. OpenAI used both to prevent GPU overload and ensure availability. Why use these? ✅Prevent DDoS attacks ✅Avoid server crashes ✅Ensure responsiveness for all users
Replies (1)
More like this
Recommendations from Medial
Karan Jot Singh
Jack of all trades, ... • 3m
Day 11 of becoming System Design Pro Still wrapping my head around rate limiting Is it a scaling issue? Algorithmic? Max-thread problem? When we already have vertical scaling, load balancing, consistent hashing.. why rate limit at all? #LearnInPu
See MoreVansh Khandelwal
Full Stack Web Devel... • 28d
Reactive systems prioritize responsiveness, resilience and elasticity; a core challenge is back-pressure—controlling data flow so producers don’t overwhelm slower consumers. Techniques include buffering to smooth bursts, rate-limiting producers, prio
See MoreVansh Khandelwal
Full Stack Web Devel... • 7m
In the rapidly evolving digital landscape, APIs (Application Programming Interfaces) serve as essential connectors among software applications, enabling seamless communication between systems. However, their accessibility also makes them prime target
See MoreNivroCorp
Your Partner in Web,... • 10d
You’re about to ship. Before you do, check these from a security perspective. These are things that break products later. Authentication Hash passwords with bcrypt. Rate limit logins. 2FA for admins. Why: weak auth becomes stolen accounts once users
See MoreSwamy Gadila
Founder of Friday AI • 7m
🚀 Should India Start Charging Fees for High-Value UPI Transactions? UPI is a world-class digital payments system — fast, free, and inclusive. But there's a hidden cost: 💸 Infra cost of ₹0.10–₹0.30 per transaction 🏦 Over ₹1,000 crore/month just t
See MoreDownload the medial app to read full posts, comements and news.












/entrackr/media/post_attachments/wp-content/uploads/2021/08/Accel-1.jpg)